VLANs for the Homelab: A beginner's guide to segmenting networks
I tried to condense the many hours I spent learning what VLANs are and how to implement them, trying to focus on the important information. If you've had a hard time understanding What a VLAN is, why you'd use it, and how you'd use it: check this out.
I tried to condense the many hours I spent learning what VLANs are and how to implement them, trying to focus on the important information.
What is a VLAN?
A VLAN is short for Virtual LAN. A VLAN is an isolated broadcast domain. If that doesn't mean anything to you, we can just call it an isolated segment or isolated part of a network, where devices on that segment can not "see" devices on other segments.
One way that has helped me to grasp this concept is thinking of mDNS or DLNA devices (another little rabbit hole to go down, but for now stick with me). Think about a wireless printer or a Chromecast. These devices usually use technology that allows them to "magically" appear on your phone if you're connected to the same network. That is because your phone (or laptop) and the Chromecast or printer are in the same broadcast domain or segment. If your laptop and your Chromecast were each in different segmented VLANs, it would be as if the Chromecast doesn't exist as far as your laptop is concerned.
Finally, a VLAN is not a subnet. This is imporant, we will touch on this in a future post about inter-VLAN routing.
So it breaks my Chromecast. Why would I want to use it?
While in the case of trying to print to a wireless printer from your work laptop, having each device in a different network segment would be annoying, there are several valid use-cases for VLAN segmentations in the homelab or home newtworking setups, including:
- Isolating work-from-home devices (like a work laptop, printer) from personal devices
- Isolating "production" servers from "staging" or "development" servers if you are running some type of application on your homelab
- Isolating IoT or untrusted devices - for example having all of your Alexa or smart home devices connected on an isolated VLAN so they can't "see" and spy on your internal network
- Ability to finely control inter-VLAN routing - this is one we will touch on later on, as VLANs allow a network administrator to establish rules for how different VLANs can interact with each other and with the internet - for example a "kids" VLAN that doesn't have access to a particular game after 10PM
VLAN-aware Switches and Routers
Before we move in to more details about implementation, I want to briefly discuss the hardware side of things. This will be a very high-level overview as there are plenty of resources for learning the actual "behind-the-scenes" of how VLANs work in networking hardware. I am aiming to make it easily understood for a newcomer or beginner.
Remember: Part of setting up VLANs is learning the quirks of your particular equipment and not to assume one vendor will be like another in their VLAN implementation. You will find different manufactures will have slightly different implementations, but the overall concept remains the same!
Why can't all routers and switches support VLANs, isn't it just a software thing?
Yes and no. At the end of the day, all a VLAN really is in practice is a tiny bit of extra information added to every "packet" of information traveling through your network. This information needs to be interpreted and treated accordingly by your equipment. This can be done in software or hardware. BUT, remember that our routers and switches are usually not very powerful when it comes to software tasks.
Network switches are low-power, efficient devices that do a simple job really efficiently with hardware. That's why a Mikrotik CRS-328 can switch 63gbps of traffic when it has a single 800 mhz CPU. The minute it needs to use its CPU to route traffic, like routing traffic from one VLAN to another, that throughput number falls to under 500 mbps.
There are 3 solutions to this problem:
- Throw more power at it: a powerful CPU can handle VLAN tagging without much issue - think about a Proxmox or other virtualization server, which can handle VLAN traffic
- Use hardware that is optimized for the task: find a "managed" switch that has Layer 2 capability if you just need simple VLAN capability or Layer 3 Hardware capability if you'd like the switch to be able to route traffic between different VLANs
- Be OK with lower speeds or decreased efficiency. This is sometimes the answer, especially for the homelab. For example, my travel router, a GL-AR750s has OpenWrt installed and is able to do VLAN filtering through software. I am fine that this isn't the most efficient setup possible and value the convenience and cost effectiveness more in this situation. This may apply to many beginners, who have a router that can just be flashed with OpenWrt and handle VLANs through its CPU. It's still the same VLAN goodness, just slower and cheaper!
VLAN terminology glossary
The following are some important terms and concepts to understand. These will help you grasp diagrams and examples of VLAN setups and translate them to your own equipment:
VLAN ID/VID:
This is the number, 1-4095 of the VLAN. This is used by networking equipment to recognize and group members of the same VLAN together. It is important to realize that the number is all that matters. If you label VLAN 10 "Sally" on one switch and VLAN 10 "Jimmy" on another, the only thing the switches really care about is the VID
Tag
A VLAN tag is a little piece of information added to a packet that tells networking equipment which VLAN that packet belongs to.
Tagged
When setting up a VLAN-aware switch, you'll often come across the word tagged or untagged in the form of a checkbox or dropdown menu for each physical port on the switch or router (and sometimes the "CPU" is considered its own port, like in the case of OpenWrt or "bridge" in the case of Mikrotik - this is important for inter-VLAN routing which will be discussed later). When selecting "tagged" - you are indicating to the switch that the traffic on that port with the VID you are marking as TAGGED should keep its VLAN tag when it leaves/enters the switch.
If a VLAN is tagged on a port and you connect a non-VLAN aware device, that traffic will be invisible to that device, while a VLAN-aware device will be able to pick up that traffic and filter it. This is useful for trunking (also defined in this list).
Untagged (access port on Cisco)
The inverse of the above, you are telling the switch that traffic with the untagged VID will have its tag removed as it leaves the switch, so it will present to the connected device as if it is regular non-VLAN traffic.
PVID
This is the physical port VID. You can think of this as the "default" VLAN ID for the port, meaning that packets coming into/leaving the switch with no tag will be considered to be part of this VLAN. You might be confused by the point of this when you also have untagged/access ports. On Mikrotik if you select a PVID for a port it will automatically show that VID as untagged on that port, without you needing to manually add it. On my TP-Link T1600G I had to choose a PVID for a port and select a port as untagged. From what I can tell reading on forums, some vendors separate egress/ingress via untagged/PVID respectively. Just know to make sure with your documentation which pattern your equipment follows.
Trunk
This is one of my favorite and what I think is the most powerful parts of VLANs, trunks. A trunk is formed when you tag multiple VIDs on a single port on one switch. This port can then be used to connect another VLAN-aware switch and be able to use the same VLANs on that switch too. A very real usage of this: I have 2 VLAN-aware switches in my network: a Mikrotik CRS-328 which is connected via a trunk port to a Mikrotik CRS-317. This allows me to use extend my network and have the extra 10G SFP+ ports on the second switch, while still keeping the same network segmentation.
What's next?
Now that you're equipped with some basic knowledge, I would recommend getting your hands on a VLAN-aware switch or installing OpenWrt on an old router and experimenting with VLANs. Here are some resources explaining VLANs on various equipment:
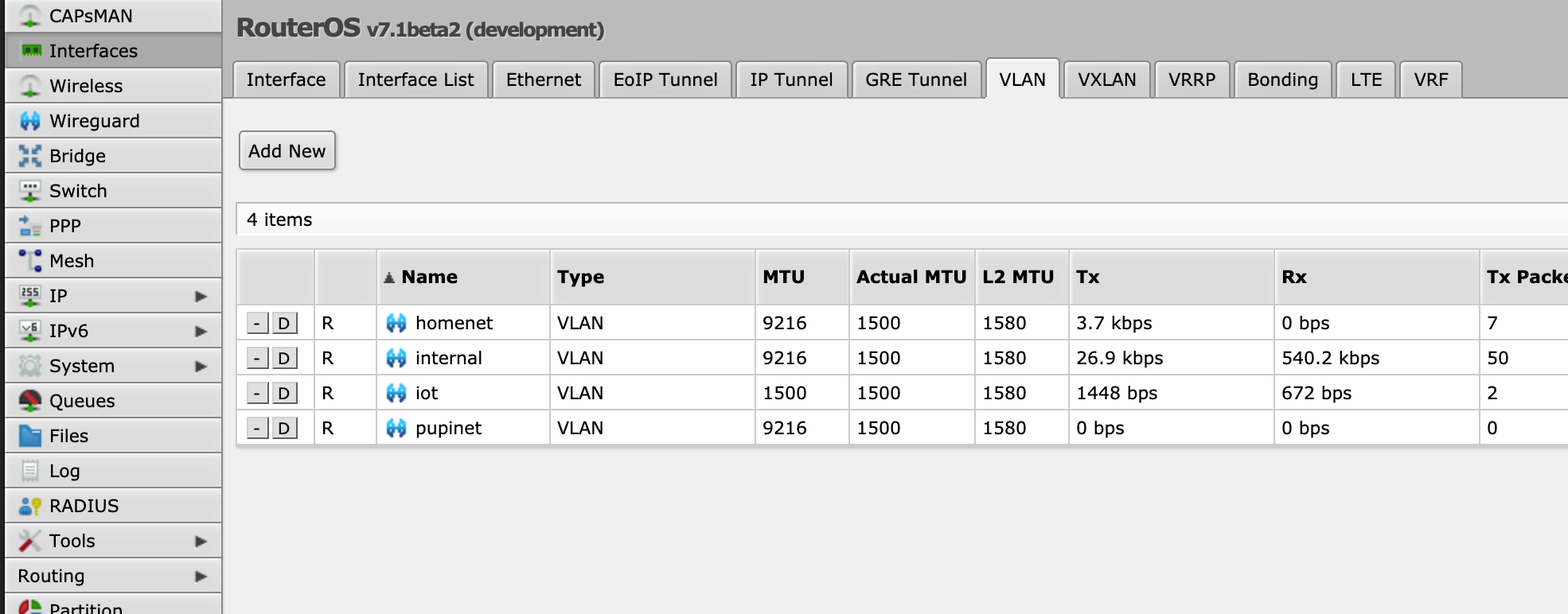
- Mikrotik: Basic VLAN Switching (router-on-a-stick)
- Mikrotik: Bridge VLAN Filtering - important for inter-VLAN routing
- Illustrations and examples for comprehending VLAN switching
Hope this was helpful to you. Please let me know if there's anything that can be added or improved here!
Please note that I only link products that I have bought and tested myself, and some of the links above are Amazon affiliate links, which I earn a commission from (at no additional cost to the buyer).
I just made an account on Twitter - so please follow me over there for future updates!
